OKEMOS – 2016 was the year hacktivists disrupted cyberspace as never before. And offline, hacker activities were much more unsettling to the international status quo. With the mix of fake news, leaked insider information to the press, and claims and counterclaims by public officials, the result was an undermining of news media and government source authority, credibility, trust and legitimacy.
The new movie Rogue One: A Star Wars Story is well-timed — epitomizing outsiders banding together to bring down the powerful enemies against long odds to steal confidential plans. This plot reminds me of hacktivist agendas over the past year.
Any summary of 2016 must start by recognizing that a global anti-establishment mood brought upsets that defied “expert” predictions — both offline and online. The surprising Brexit vote, Donald Trump’s shocking election victory and Italy’s “no” vote in a referendum on constitutional reform are a few of the noteworthy examples of how this “anti” trend shocked the world in successive major events led by populist uprisings.
And online, activist hackers, often called hacktivists engaged in a long list of different acts of hacktivism — even prior to the election, took center stage in supporting (or opposing) a vast array of causes that range from anti-Wall Street to anti-free trade to anti-corruption to anti-fill-in-the-blank. This is not just about distributed denial of service (DDoS) attacks, but stealing data in a variety of ways — for their causes.
As I write this blog, questions are swirling about election hacking, who knew what and when, Russian involvement and motives in picking winners and losers, President Obama’s promised retaliation, and much more. What is clear is that this huge end-of-the-year hacking story will bleed well into 2017 and beyond. No one is saying that the actual polling machines or votes cast in the election were hacked, but the focus is on influencing public opinion with DNC emails.
“Hackers will hack” for a plethora of reasons, and plenty of black hats were (and still are) trying make a buck or two via old-fashioned online robbery, extortion and stealing credentials from Yahoo and many others. Still, the top hacker impacts revolved around politics and wealthy people being exposed for hiding money in offshore accounts in the Panama Papers — which some experts called history’s biggest data leak ever.
From Clinton campaign emails revealed by WikiLeaks to DDoS attacks against governments, banks and other corporations, the dark side of the Web never slept in 2016.
Even the sport of cricket was the source of hacktivism in India and Pakistan, with additional hacking of the rich and powerful by lesser known hacktivists. The mainstream media also saw personal data about them released, which left many leaders feeling uncomfortable as more people became hackers who made their mark through digital disobedience.
QUICK RECAP: TOP 7 CYBER STORIES FOR 2016
Following 2015, when data breaches started to become much more personal, the top cybertrend in 2016 was hacktivism. Specifically, the uncovering of hidden information went into hyper-drive — with groups like Anonymous, WikiLeaks and DC Leaks shaping the news and impacting global dialogue, while undermining trust in digitally stored information. Much more on this No.1 trend below.
Second was the growth in ransomware attacks. The overall numbers were up a staggering 6,000 percent according to IBM — with hospitals, governments and many others experiencing major cyber incidents.
As CNBC reported: “The problem is, the business model works: 70 percent of business victims paid the hackers to get their data back, the study found. Of those who paid, 50 percent paid more than $10,000 and 20 percent paid more than $40,000. …”
Third, overall data breach numbers and incidents remained high.Yahoo topped the list, with announcements about two huge breaches that actually happened a few years back.
“Internet giant Yahoo announced a massive data breach Wednesday that affected over one billion accounts, making it by far the largest data breach in history. This follows the disclosure in September of a different breach that affected more than 500 million of the company’s customers,” PC World reported. “What stands out with this new security compromise is that it occurred over three years ago, in August 2013, and that hackers walked away with password hashes that can be easily cracked.”
Other notable data breaches in 2016 occurred with Olympic athletes, the IRS, Wendy’s, Medstar and the Justice Department. See this list for more 2016 examples.
Fourth, Distributed denial of service (DDoS) attacks brought down large parts of the Internet using Internet of Things devices. Popular Mechanics magazine describes How hackers wrecked the Internet using DVRs and Webcams:
“The current assault against Dyn is one of the simplest in a hacker’s playbook. The distributed denial of service attack (DDoS) doesn’t require breaking into a target’s computers or finding any secret weakness. Instead, it involves simply pummeling them with so much traffic they can’t possibly keep up. Hackers executing a DDoS call upon millions of machines under their control and command them to ask the target for so many things all at once that the target all but melts down under the strain.”
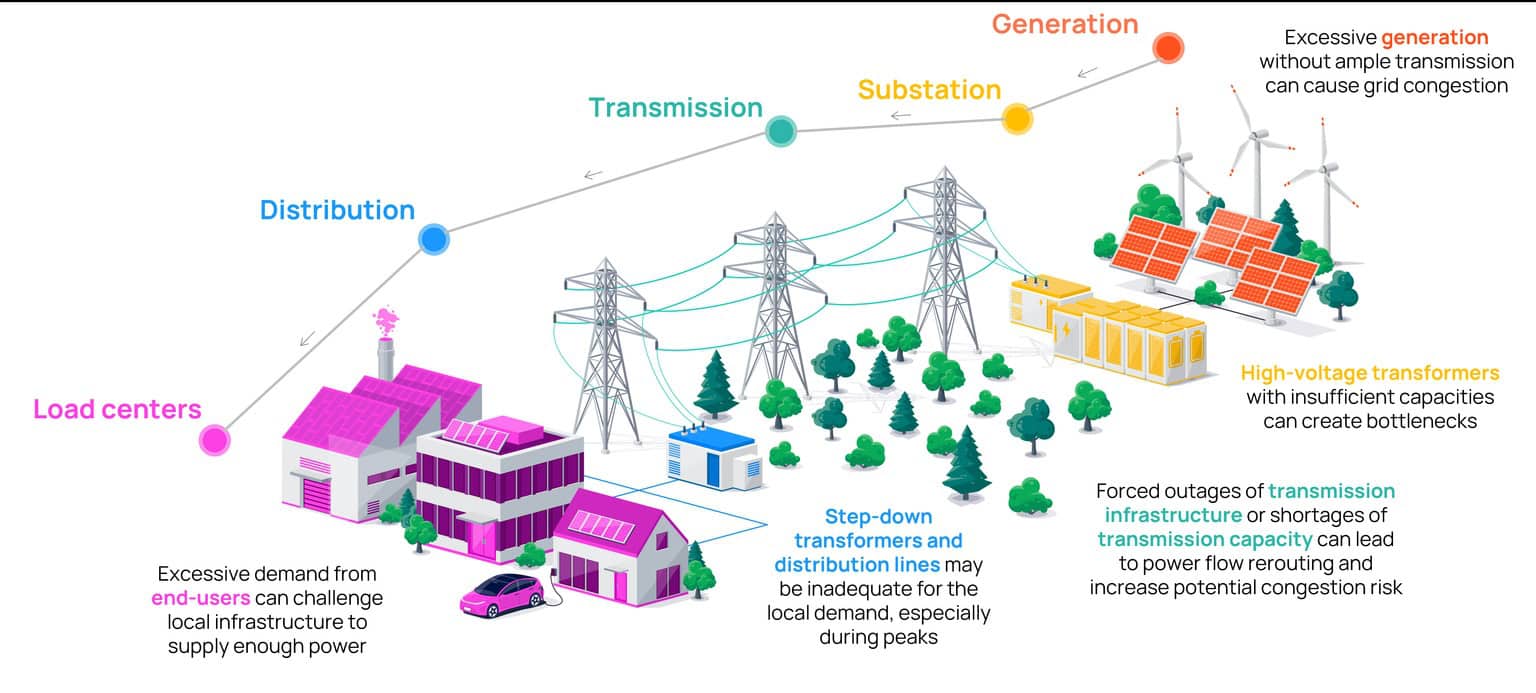
Fifth, Power grids and other significant infrastructure cyberattacks made headlines. In Ukraine, the damage and impact was unprecedented, Wired reported:
“The hackers who struck the power centers in Ukraine — the first confirmed hack to take down a power grid — weren’t opportunists who just happened upon the networks and launched an attack to test their abilities; according to new details from an extensive investigation into the hack, they were skilled and stealthy strategists who carefully planned their assault over many months, first doing reconnaissance to study the networks and siphon operator credentials, then launching a synchronized assault in a well-choreographed dance.”
Sixth, the so called “Apple vs FBI encryption battle” portends future arguments over privacy of data versus national security. This article summarizes the different perspectives.
“The case marked one of the highest-profile clashes in the debate over encryption and data privacy between the government and a technology company,” the article states. “Law enforcement authorities say that encryption used by the likes of Apple makes it harder for them to solve cases and stop terrorist attacks.
“Technology firms have kicked back, saying that encryption is key to protecting user data from hackers.”
Seventh, whaling and online fraud schemes make social engineering attacks a top FBI issue for cybercrime. There were many stories about the people side of cyber fraud, one of which highlights whaling (phishing 3.0), while another, below, points to social engineering attacks.
In April 2016, the Phoenix Division of the FBI formally warned businesses about the dramatic increase in business email compromise scams. According to the FBI press release:
“The schemers go to great lengths to spoof company email or use social engineering to assume the identity of the CEO, a company attorney or trusted vendor. They research employees who manage money and use language specific to the company they are targeting, then they request a wire fraud transfer using dollar amounts that lend legitimacy. …”
And for a bonus item (something that didn’t happen), there were no cyber 9/11 or crippling Internet surprise that lasted days. Yep —this item is actually good news. Most technology worked well, and we recovered well from security and infrastructure outages. (While some want to see Russian hacking here or other nation-state cyber battles, I am grouping those still-debated topics under No. 1 — with more to come on that front below.)
For those of us in the front lines of cybersecurity battles each and every day, it is easy to forget that many technology advancements are happening all around us. For example, this MIT Technology Review for 2016 lays out major tech breakthroughs including advancements from autonomous cars to genes to robots communicating with other robots.
MORE DETAILS ON THE TOP CYBER STORY AND TREND GOING INTO 2017
Now back to No. 1. On the world stage, hacktivism grabbed the microphone in 2016.
What is hacktivism (also spelled “hactivism” by some)? Simply stated, it is the subversive use of computers and computer networks to promote a political or social agenda.
No doubt, some will say that many of these hacks were sponsored by major world powers such as Russia. Foreign government involvement is likely the case, but there is disagreement in the intelligence community over who was behind which hacks in 2016 and what their motives were.
As a side note, the Russian government continues to deny involvement in meddling in the U.S. election, and WikiLeaks says its source was not the Russian government. This article from Andrew P. Napolitano makes the case that the data was leaked from Washington insiders. I am not sure who is correct.
Regardless of who all the players were, the unmistakable hacktivism trend is still the same. Hacking is no longer just for dollars, and this trend has been growing for several years to land at the top spot.
Why Compare ‘Hackers With A Cause’ To The New Star Wars Movie?
In Rogue One: A Star Wars Story, unknown rebels accomplish unpredicted results. Yes, the story is science fiction, but the similarity lies in the way hackers stole center stage from powerful establishment organizations that were overconfident in 2016.
“In a time of conflict, a group of unlikely heroes band together on a mission to steal the plans to the Death Star, the Empire’s ultimate weapon of destruction. This key event in the Star Wars timeline brings together ordinary people who choose to do extraordinary things, and in doing so, become part of something greater than themselves.”
This could very well describe the global hacktivists view of the world in 2016. (Note: the “Death Star plans” are synonymous with any data, plan, information or emails that hackers deem are relevant to achieving their wider cause.)
Or, if you don’t like science fiction, our new world of global hacktivism is depicted in the TV Show Mr. Robot.
Regardless of whether you can relate to any of these cyber analogies, hacking for a cause is set to explode into a complex set of state and local government challenges.
Final Thoughts On The 2016 Year in Cyber
What have we learned over the past year? Sadly, we are not winning more global cyber battles. The hacker bad guys are still outgunning the good guys.
While many cyberdefenses are improving in global enterprises, the number of bad actors is also growing rapidly. As the list above shows, the breadth and depth of cyber threats and online vulnerabilities continues to grow online — especially with new Internet of Things (IoT) devices coming onto the market.
The U.S., our allies and foreign adversaries are increasingly engaging in sophisticated cyberbattles that equate to a cyber cold war and cybersecurity arms race. New relationships, partners in cyberspace and causes are evolving in unpredictable ways, and third-world hackers are teaming with first-world experts to achieve desired results.
What’s troubling to me is the new thinking that is emerging regarding right, wrong and ethics in cyberspace — with hacktivists all around the world. The mix of fake news, misinformation, ransomware websites that come and go, and other hacker dirty tricks results in a diminishing of the public’s trust and legitimacy of data — both online and offline. This trend is impacting governments, the mainline news media, private corporations and global relationships.
A new world of hacking motives and causes is starting to emerge — along with convenient, easy-to-use tools for computer novices to do many dangerous things online.
God only knows what “Death Star plans” the hacktivists will go after next.