ANN ARBOR – Cybersecurity experts Dan Lohrmann and Richard Stiennon provide details on how the Russians hacked the Solarwinds networking software used by US government and nearly all the Fortune 500 companies in America.
Russia’s hack of IT management company SolarWinds began as far back as March, and it only came to light when the perpetrators used that access to break into the cybersecurity firm FireEye, which first disclosed a breach on December 9. Since then, a cascading number of victims have been identified, including the US Departments of State, Homeland Security, Commerce, and the Treasury, as well as the National Institutes of Health. The nature of the attack—and the tremendous care taken by the hackers—means it could be months or longer before the extent of the damage is known. The impact is already devastating, though, and it underscores just how ill-prepared the US was to defend against a known threat—and to respond. It’s also ongoing, Wired magazine reported.
Dan Lohrmann – Chief Strategist & Chief Security Officer – Security Mentor

Dan Lohrmann
* Lead efforts to define and develop key strategic initiatives for the company’s award-winning security awareness training offerings.
* Provide thought leadership regarding cybersecurity and online privacy trends in public and private sectors.
Lohrmann was Michigan’s first Chief Security Officer (CSO) & Deputy Director within Michigan’s Department of Technology Management & Budget (DTMB). Dan oversaw all aspects of cybersecurity, physical security, department emergency management, and critical infrastructure protection within state government.
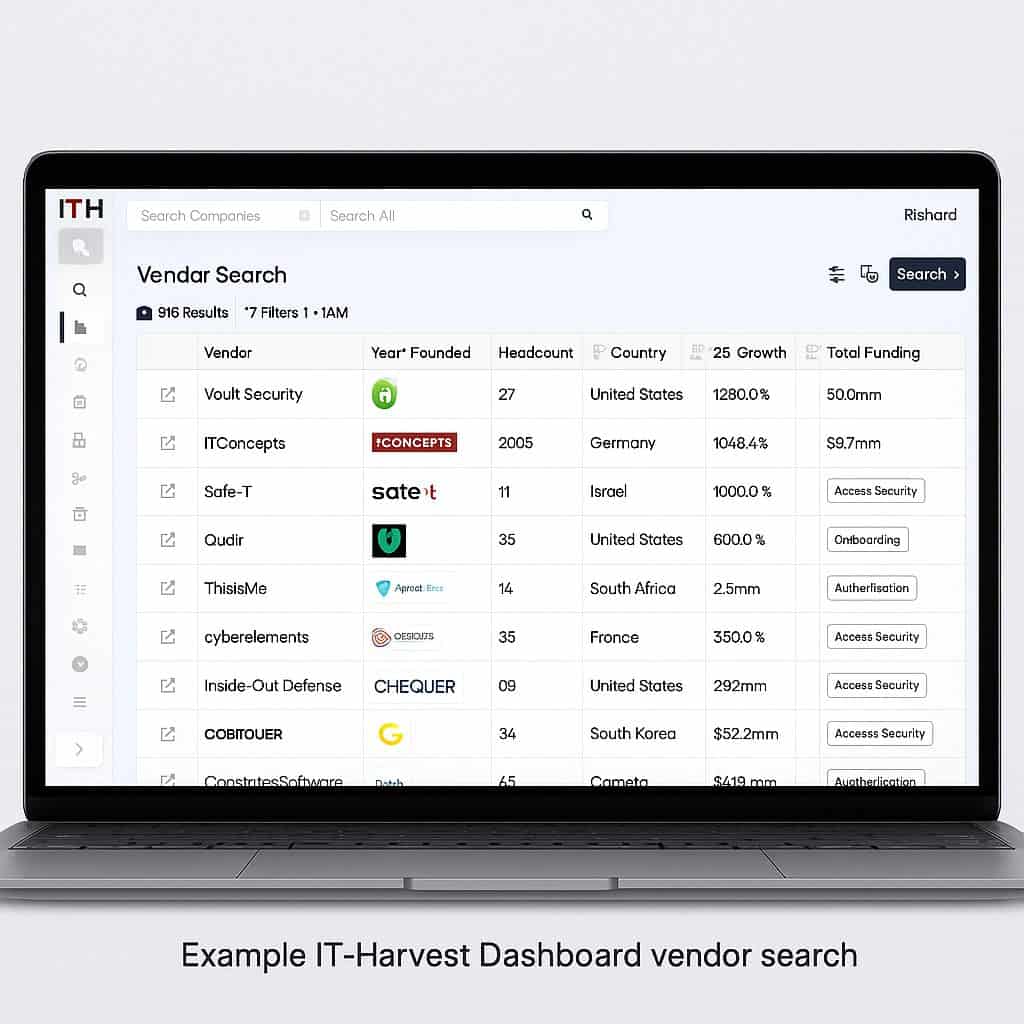
Richard Stiennon, Chief Research Analyst, IT-Harvest
6 Publications
CyberWar and the Malware Blame Game
There Will Be Cyberwar
HeartBleed Discussion with Richard Stiennon
UP and to the RIGHT: Strategy and Tactics of Analyst Access
Richard Stiennon & Bill Conner Discuss State of the Cybersecurity Industry
Surviving Cyberwar