From auto suppliers to hospitals, a new wave of AI-driven vulnerabilities could overwhelm defenses—experts warn
BIRMINGHAM – Cybersecurity is entering a phase few businesses are prepared for—and the consequences could hit Michigan’s economy hard.
In an interview with MITechNews, cybersecurity analyst Richard Stiennon, founder of IT-Harvest, described what he calls a “break-glass moment” for the industry: artificial intelligence is now capable of discovering—and even chaining together—software vulnerabilities at a speed that outpaces traditional defenses.
At the same time, a new framework from the Cloud Security Alliance warns of an “AI vulnerability storm,” where the number of exploitable flaws could surge beyond what companies can realistically manage.
For Michigan—home to global manufacturing, healthcare systems, and a growing tech sector—that shift could have far-reaching implications.
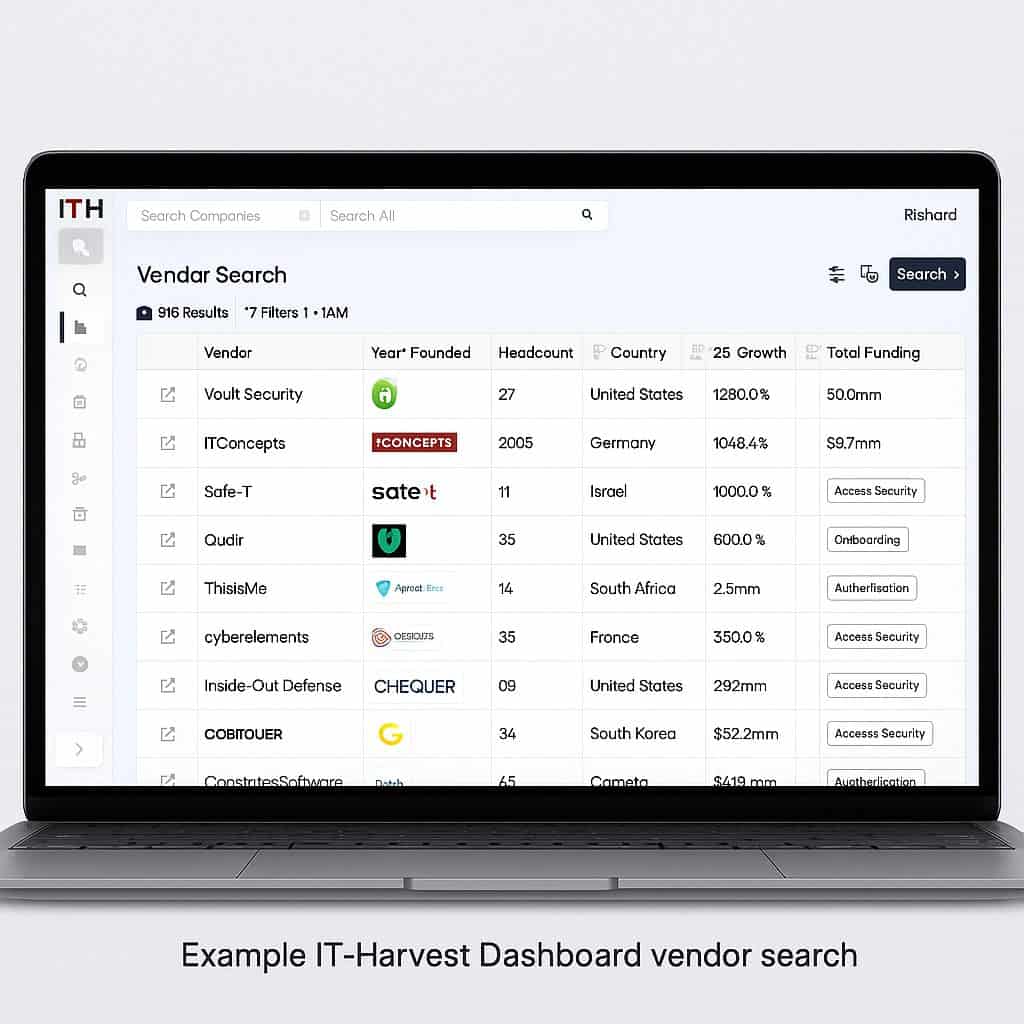
You can get a Free demo of Richard Stiennon’s Cybersecurity Dashboard that lists more than 4,000 cybersecurity vendors and more than 12,000 products. If you purchase a seat, use code 919 to receive a discount from MITechNews.Com
AI System Built for Scarcity—Now Facing Abundance
For decades, cybersecurity has operated under a basic assumption: vulnerabilities were relatively limited, and the challenge was finding and fixing them before attackers did.
AI is flipping that model.
New AI systems are now capable of rapidly identifying thousands of previously unknown software flaws—often referred to as “zero-day vulnerabilities”—and, more concerning, linking them together into complex attack paths.
“That changes everything,” Stiennon said. “We’re moving from a world where vulnerabilities were scarce to one where they are abundant.”
That shift creates a dangerous imbalance.
Security teams are already stretched thin. If AI accelerates vulnerability discovery faster than companies can patch systems, the backlog could grow exponentially—creating persistent exposure across networks.
Why Michigan Is Especially Exposed
Michigan’s economy makes it particularly vulnerable to this next phase of cyber risk.
The state’s automotive and manufacturing sectors rely heavily on interconnected supply chains, legacy systems, and industrial control networks—many of which were not designed with modern cybersecurity threats in mind.
A single vulnerability in a supplier’s software could ripple across multiple companies.
Hospitals and healthcare providers face similar risks. Ransomware attacks have already disrupted care delivery nationwide. An AI-driven surge in vulnerabilities could make those attacks more frequent—and more sophisticated.
Small and mid-sized businesses, which make up the backbone of Michigan’s economy, may be the most exposed of all.
Many lack dedicated cybersecurity teams and rely on off-the-shelf solutions that may not keep pace with rapidly evolving threats.
The Industry Response: ‘Mythos-Ready’ Security
Recognizing the scale of the problem, the Cloud Security Alliance has released new guidance urging organizations to become “Mythos-ready”—a reference to emerging AI capabilities reshaping the threat landscape.
The framework signals a fundamental shift in thinking.
Instead of focusing solely on prevention, organizations must assume vulnerabilities will exist—and design systems that can withstand continuous exposure.
That includes:
- Prioritizing rapid detection and response
- Reducing the time it takes to patch critical systems
- Building resilience into infrastructure rather than relying on perimeter defenses
In other words, cybersecurity is moving from a model of control to one of containment and recovery.
A Fragmented Industry—and a Growing Challenge
As threats evolve, so does the cybersecurity industry itself.
Thousands of companies now offer solutions across dozens of categories, from endpoint protection to cloud security, identity management, and AI-driven threat detection.
For business leaders, that creates a new problem: knowing where to turn.
“There are so many vendors, so many tools—it’s incredibly difficult for organizations to understand who does what,” Stiennon said.
To address that complexity, IT-Harvest has developed a comprehensive cybersecurity dashboard that maps the global ecosystem of vendors and their products.
The platform tracks thousands of companies, categorizing them by function and capability, and providing a clearer picture of how the industry is evolving in real time.
Why Visibility May Be the Most Important Defense
In a world where vulnerabilities are multiplying, visibility into the cybersecurity landscape is becoming critical.
Organizations are no longer just defending against attackers—they are navigating an increasingly complex marketplace of solutions.
Choosing the wrong tools—or failing to integrate them effectively—can leave gaps that attackers exploit.
“The challenge isn’t just stopping threats anymore,” Stiennon said. “It’s understanding the entire ecosystem well enough to build a defense that actually works.”
That insight may be especially relevant for Michigan companies, many of which are balancing digital transformation efforts with legacy infrastructure.
A Race Against Time
Ultimately, the emerging reality is a race between two forces:
- AI systems discovering vulnerabilities at machine speed
- Organizations trying to fix them before they are exploited
Right now, that race appears uneven.
If the gap continues to widen, cybersecurity could shift from a manageable risk to a systemic one—affecting not just individual companies, but entire industries.
For Michigan, the stakes are high.
The state’s economic strength is tied to sectors that depend on reliable, secure systems. A surge in cyber vulnerabilities could disrupt operations, increase costs, and expose sensitive data across supply chains.
Cybersecurity is no longer just a technical issue—it’s a strategic business risk.
AI is accelerating both sides of the equation, but for now, it appears to be giving attackers the advantage.
The question is whether companies can adapt quickly enough.
Because in this new environment, it’s not just about preventing the next attack.
It’s about surviving a world where vulnerabilities are everywhere—and increasing by the day.
If you’d like to get a demo of Richard Stiennon’s Cybersecurity Dashboard that lists more than 4,000 cybersecurity vendors and more than 12,000 products. If you purchase a seat, use code 919 to receive a discount.