SAN FRANCISCO – More than half a million routers and network devices in 54 countries have been infected with sophisticated malware, researchers from Cisco’s Talos Intelligence Group warn.
The malware, which the security researchers are calling VPNFilter, contains a killswitch for routers, can steal logins and passwords, and can monitor industrial control systems.
An attack would have the potential to cut off internet access for all the devices, William Largent, a researcher with Talos, said Wednesday in a blog post.
Late Wednesday, the FBI received court permission to seize an internet domain that the Justice Department says a Russian hacking group, known as the Sofacy Group, was using to control infected devices. The group, which also goes by the names Apt28 and Fancy Bear, has targeted government, military and security organizations since at least 2007.
“This operation is the first step in the disruption of a botnet that provides the Sofacy actors with an array of capabilities that could be used for a variety of malicious purposes, including intelligence gathering, theft of valuable information, destructive or disruptive attacks, and the misattribution of such activities,” Assistant Attorney General for National Security John Demers said in a statement.
Attacks on routers strike a nerve not only because they can halt internet access, but also because hackers can use the malware to monitor web activity, including password use. In April, US and UK officials warned about Russian hackers targeting millions of routers around the world, with plans to carry out massive attacks leveraging the devices. In that announcement, the FBI called routers a “tremendous weapon in the hands of an adversary.”
“Quite anything is possible, this attack basically sets up a hidden network to allow an actor to attack the world from a stance that makes attribution quite difficult,” Craig Williams, Talos’ director, said in an email.
VPNFilter has infected routers in Ukraine in particular at an “alarming rate,” with a spike in infections in the Eastern European country on May 8 and May 17. Talos said the malware could be used in a future attack on the country. The researchers said the new malware shares many of the same codes used in known Russian cyberattacks and called the attack “likely state-sponsored.”
Talos researchers are still looking into how the malware infects routers but said that routers from Linksys, MikroTik, Netgear and TP-Link are affected.
Netgear said it’s aware of VPNFilter and was advising its users to update their routers.
“Netgear is investigating and will update this advisory as more information becomes available,” a spokesman said in an emailed statement.
MicroTik acknowledged that Cisco had informed it about a malicious tool found on three devices it made, and said it had already applied a patch to close up the vulnerability through which the malware was installed. “Simply upgrading RouterOS software deletes the malware, any other 3rd party files and closes the vulnerability,” a spokesman said.
The other two network companies didn’t respond to a request for comment.
The researchers released their findings now out of concern over a potential upcoming attack against Ukraine. The country has repeatedly been the victim of Russian cyberattacks, including the NotPetya ransomware, which US and UK officials have called the “most destructive cyberattack ever.”
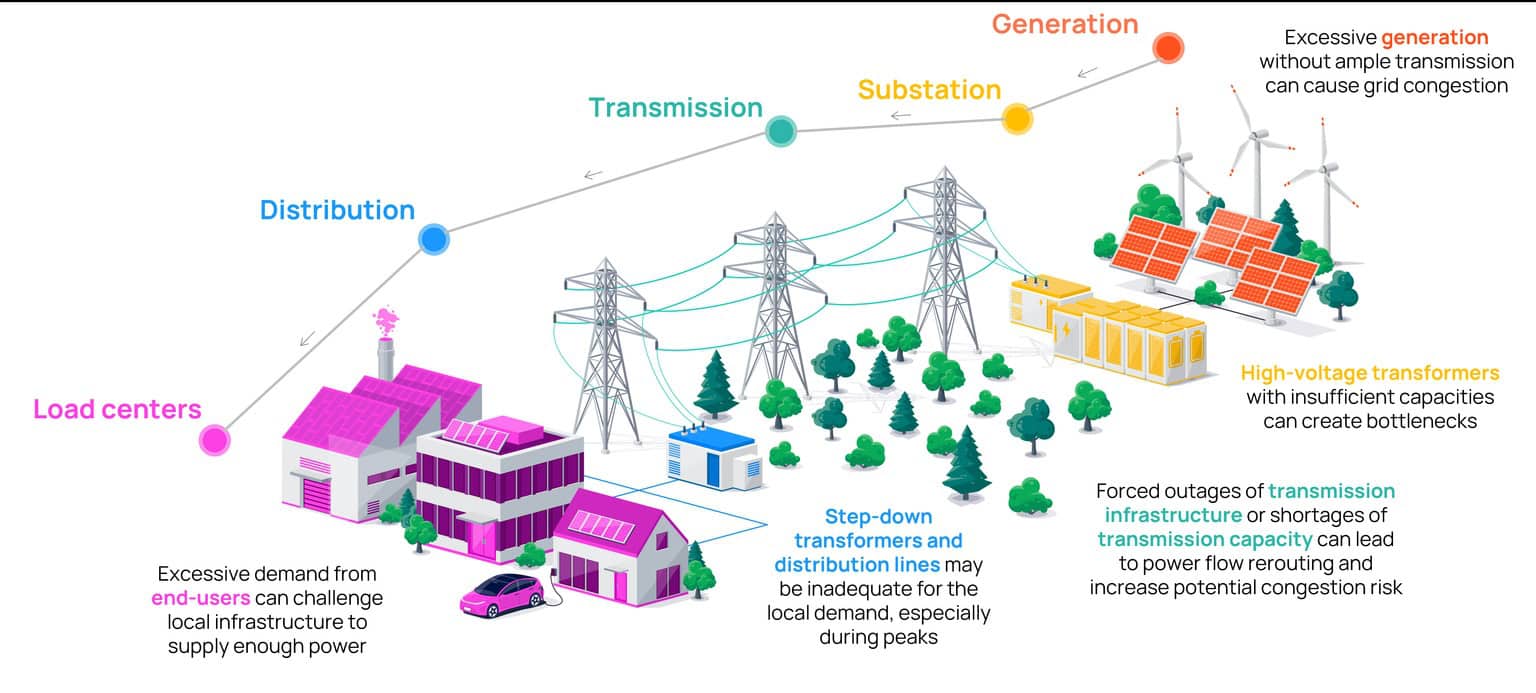
Researchers also attributed to a 2016 blackout in Ukraine to Russian hackers who used malware to target industrial control systems.
The Cyber Threat Alliance, which Cisco is a member of, has briefed companies about the destructive malware, calling VPNFilter a “serious threat.”
“It has destructive capability. The malware’s flexible command structure gives the adversary the ability to use it to ‘brick’ these devices. That’s not a capability usually built into malware like this,” Cyber Threat Alliance President Michael Daniel said.
Talos is recommending that people reset their routers to factory defaults to remove the potentially destructive malware and update their devices as soon as possible.